Needing an anonymous way to sign up for something online? You might want to look into a throwaway email account. These accounts are created specifically for single-use situations, like signing up for free trials that you don't wish to keep long-term.
A throwaway email account gives you increased privacy by separating your main email address from possibly malicious sites and services.
- Throwaway emails are often used for:
- Registering for online forums
- Protecting your main email from spam
- Renting a hotel room anonymously
A Pseudonymous Digital Persona
In the ever-expanding virtual sphere, individuals often crave a sense of discretion. This desire has fueled the concept of an anonymous online identity, a persona that allows users to express themselves freely from their real-world counterparts.
The allure of anonymity draws many to construct elaborate online identities, frequently separate from their true selves. Individuals may assume pseudonyms, create tales, and even modify their digital appearances.
The motivations for adopting an anonymous online identity are varied. Some seek to shun societal pressures, while others hope to vent their thoughts without reservation. Still, others exploit anonymity for malicious purposes.
The ethical and societal implications of anonymous online identities continue to be debated in the digital age.
Secret Correspondence Channel
In the labyrinthine world of espionage, a trusted communication channel is paramount. A secret correspondence system acts as the lifeline for clandestine operations, allowing operatives to share vital data while evading detection. This intricate network often involves coded messages, false identities, and real-world meetups conducted in deserted locations.
- Once upon a time , such channels relied on dead drops to transmit messages, but the advent of technology has brought new and complex methods.
- Today, online platforms provide masked platforms for operatives to communicate.
- Moreover, the use of steganography can further hide the true content of messages.
Maintaining a secure correspondence channel is a constant challenge, requiring vigilance and adaptation to evolving threats. Any failure in security can have catastrophic consequences for an operation.
Provisional Communication Link
A interim communication link is established in order to establish contact between two parties when a permanent connection has been disrupted. These links are often employed for critical scenarios where stable communication is essential for coordination. They can also be utilized in remote areas where establishing a conventional link is infeasible.
The establishment a temporary communication link more info often involves radio frequency devices to transmit messages over long ranges.
Note that the effectiveness of a temporary communication link depends on factors such as interference levels and the frequency of the equipment used.
A Mysterious Sender's Address
Sometimes, you might receive correspondence with/from/featuring an address that appears to be fabricated/unidentifiable/undetectable. This situation/scenario/circumstance can cause/bring about/lead to a range/variety/selection of concerns/worries/feelings.
It's important/essential/crucial to remember that an unidentified sender's address doesn't necessarily/always mean the mail is dangerous/suspicious/harmful. There are several/various/numerous possible explanations, including/such as/like someone making a mistake/typing incorrectly/using a false address.
If you receive/encounter/come across mail with an unidentified sender's address/from an unidentifiable source/featuring an unknown address, it's best to exercise caution/be careful/proceed with care.
A Virtual Identity
A digital pseudonym is a fabricated name or identity used in the digital realm. It serves to enhance privacy, allowing individuals to express themselves freely. Pseudonyms can range from simple usernames to elaborate fictional personas, creating a safe space for interaction and self-exploration.
 Edward Furlong Then & Now!
Edward Furlong Then & Now!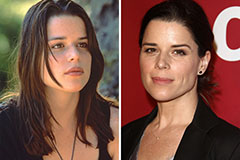 Neve Campbell Then & Now!
Neve Campbell Then & Now! Brandy Then & Now!
Brandy Then & Now! Melissa Joan Hart Then & Now!
Melissa Joan Hart Then & Now!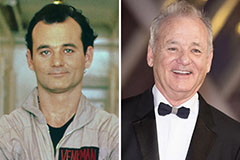 Bill Murray Then & Now!
Bill Murray Then & Now!